Cybersecurity has always been a challenge for Information Security (IS) professionals. There was a time when cybercriminals had the upper hand, as they deployed sophisticated attack strategies against scarcely-protected enterprise information and data assets. The IS community always responded in reactive mode to those threats and attacks. But, thanks to Quolab’s implementation of the MITRE ATT&CK framework, cyberthreat professionals now have a seamless set of information security tools to defend their critical digital infrastructure.
Overpowering Cyber Bullies
By some estimates, by 2023, organizations will spend an estimated $1.63 billion on securing their cloud-based information and data assets. That’s a 26.5% compound annual growth rate (CAGR) from the $636 million spent in 2020. This proves that, globally, businesses and governments are taking the cyber threat seriously. The challenge, however, has always been: How does the world respond to cyber bullies?
The answer: MITRE ATT&CK®!
Until 2013, IS professionals responded to instances of cyber-attacks after the fact. By then, the damage had already been done, and sensitive data assets were compromised. The world needed to implement a playbook that preempted instances of cybercrime. It wasn’t enough that IT professionals cleaned-up after the fact. They needed a way to detect patterns of bully behavior, that could then inform cyberthreat prevention strategies to overpower cyber bullies.
The Framework Explained
The MITRE ATT&CK framework provides just such a tool!
Contrary to popular misconception, MITRE does not represent the Massachusetts Institute of Technology Research and Engineering. It is, in fact, a government-funded research organization located in Bedford, MA, and McLean, VA.
MITRE conducted extensive research, through its Fort Meade Experiment (FMX), that successfully emulated the behavior of cybercriminals (adversaries), and those of cyber defenders. The Framework evolved using a complex set of behavioral analysis principles, and telemetry sensing.
When you know what to look for in a potential adversary, how they operate, and what the telltale signs are, of their activities; then it’s relatively easy to deal with the fallout, or even prevent and mitigate future attacks. So, what does the Framework accomplish? It systematically categorizes behavior patterns of known cyber incidents, and uses a standard set of taxonomy to facilitate inter/intra-organization communication when effectively dealing with those threats.
Facilitating the Use of Cybersecurity Tools
IS professionals have their hands full with myriads of essential tasks. And even with many of the currently available conventional tools of the trade at their disposal, it’s still a challenge to effectively deal with the aftermath of an attack, or mitigate the risks associated with one. And that’s where intuitively-designed tools play a huge role.
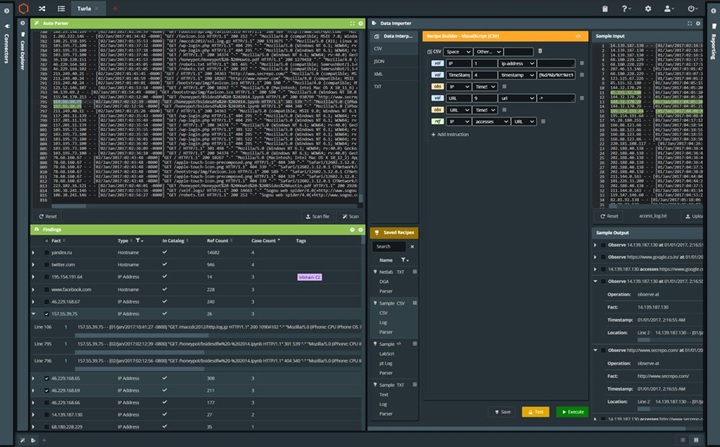
Built by a diverse group of cyber operators, software engineers, data scientists and analysts, devoted to providing innovative solutions to big/complex data management, visualization, analysis and sharing challenges, QuoLab’s Platform helps to enrich, normalize, and automate MITRE ATT&CK datasets. Built-in functionality, such as:
- automated content extraction
- advanced malware and function analysis
- tag propagation
- observation mapping of historical events
- detailed link (killchain) analysis
- custom analytics…and much more
…make harnessing the invaluable resources, contained within the Framework’s datasets, simple and intuitive. Visually powerful case management, as well as intuitively-designed automated alert functionality adds to the ease of use of this powerful Platform. Now, instead of scouring terabits of MITRE ATT&CK framework data, to uncover how bd Cyber actors behave, or what they’re planning, cybersecurity professionals can use the customized dashboards provided by the Platform to manage their security threat landscapes more efficiently.